Data / Switzerland
“We connect data centers in the U.S. as well as Switzerland”
Phoenix Systems offers tailored software and hosting infrastructure from one source.

Thomas Taroni, Co-founder, Chairman and CTO of Phoenix Systems ©Phoenix Systems
By intertwining both components, they can generate unparalleled efficiencies and security for your business, as Thomas Taroni, Chairman of Phoenix Systems, explains.
In such a dynamic field, what are your competitive advantages?
We are coming from the big data space, and we are aware of the importance of rock-solid infrastructure. That’s why we decided to partner with IBM because of their mainframe technology, which can handle massive workloads. Our main expertise is in the development of microservices architecture, and our proprietary software is run on IBM LinuxONE servers. This partnership is crucial for our success and future growth, and we have been doubling in size most years since 2015.
We have data center partners around the globe. We don’t own them but control, on behalf of our clients, all relevant processes such as installing the hardware and hypervisor and running our services, assuring confidential computing.
Most global clients use a combination of clouds from different providers. We attach the missing parts through a confidential computing* product where specific codeware is required to ensure banking or military level security. This is a major growth field for the future.
Will we reach a point where systems are impossible to crack?
I believe that every system is hackable, somehow. The crucial thing is to delay this to a point where it’s no longer relevant. Many believe that blockchain is anonymous but if it is connected to a wallet with someone’s name, transactions can ultimately be traced.
Confidential computing is important today for everyone who uses the internet. Soon, people will have to manage their own private key. Apple recently announced plans to eliminate the password, replacing it with a similar concept, and technology is moving in this direction. This solution can work, but the degree of public acceptance remains to be seen.
What is your experience of working with U.S. stakeholders?
We connect data centers in the U.S. as well as Switzerland, and we have set up local companies to conduct our business. A group structure with companies in both countries makes things seamless, with just a small delay in connectivity because of the long distances.
Importing products into the US means lowering encryption levels because of state requirements, but as software producers, we implement such regulations automatically.
The business culture is also different. Switzerland is more low-key, but I prefer the American “I want to win” mindset, since I am confident of our growth. In Switzerland, I appreciate the engineering excellence and intelligence granted to develop products before bringing them to market. I try to combine the best of both worlds.
How do you envision the company’s future growth?
My brother and I started with one server in our home 12 years ago; today we work through three data centers in Switzerland, one in Washington DC, one in Dallas, one in Hong Kong and one in Singapore. Our initial focus was on research around big data, and we really started to grow in 2015.
We manage specific sections in the data centers we operate from, creating a network that can scale rapidly. Together with the IBM centers, this allows us to diversify geographically. The secure deployment model we developed in Switzerland can be replicated globally. We recently started operations in Amsterdam and, in general, reinvest our money to finance the growth of our companies.
Despite our growth, we kept a start-up spirit: we feel we can invent the next big thing. If everything goes according to plan, at some point we will need to raise capital because, instead of 10 or 100 new servers, we will be looking at buying 10,000 and running an entire server farm. Going public is one option, but there is no plan yet and we have been growing organically for the last few years.
How can the innovative power of blockchain benefit various sectors?
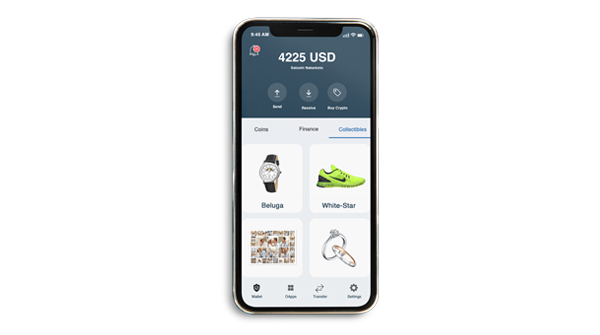
As technology evolves, we are witnessing a transformation of physical possessions to digital assets across all industries. This is especially evident in the luxury sector, where certificates are crucial in safeguarding quality and authenticity of products.

©Phoenix Systems
With one of our brands, KORE Technologies, we developed LuxID, a one-stop-shop solution through which the luxury goods companies can transition from the world of physical to digital certificates. As a technical bridge between luxury brands and the relevant blockchain protocols, KORE ensures seamless integration with existing enterprise systems in a secure and user-friendly manner.
How does the digital certificate work?
This certificate of ownership is recorded on the blockchain where not only the ID of the buyer is recorded but also that of the object, as well as information pertaining to when an asset was bought along with a timestamp. Blockchain accomplishes all of this anonymously, so that there is no room for fraud, forgery, and stealth.
©Phoenix Systems
Storing real-world assets in a digital format enhances the level of immutable transparency and enables luxury brands to bring down knock-offs, but also keep the high-priced, better-quality fakes at bay. Through credible and transparent information, customers will be able to sell, collect, and buy items with one-hundred percent certainty that their purchase is one-of-a-kind, sourced from sustainable practices, and created by people who take pride in their brand. This will also open new business avenues and empower brands to target new markets.
*Confidential computing is a cloud computing technology that isolates sensitive data in a protected CPU enclave during processing. The contents of the enclave – the data being processed, and the techniques used to process it – are accessible only to authorized programming code, and invisible and unknowable to anything or anyone else, including the cloud provider.
